The device must have a RADIUS configuration and be connected to the Cisco secure access control server (ACS). For more information, see the User Guide for Secure ACS Appliance 3.2. Information About Configuring MAC Authentication Bypass. Overview of the Cisco IOS Auth Manager, page 2. Standalone MAB, page 2 Overview of the Cisco IOS Auth.
What Is Forescout
ON THIS PAGE
- Network access control (NAC): Forescout SecureConnector Ensuring that computers meet UCSF’s minimum security standards is critical to keeping a sprawling enterprise like UCSF secure. Computers without critical security patches, anti-virus software or host-based firewalls are targets for hackers and can be used to spread malware and compromise other devices on the network.
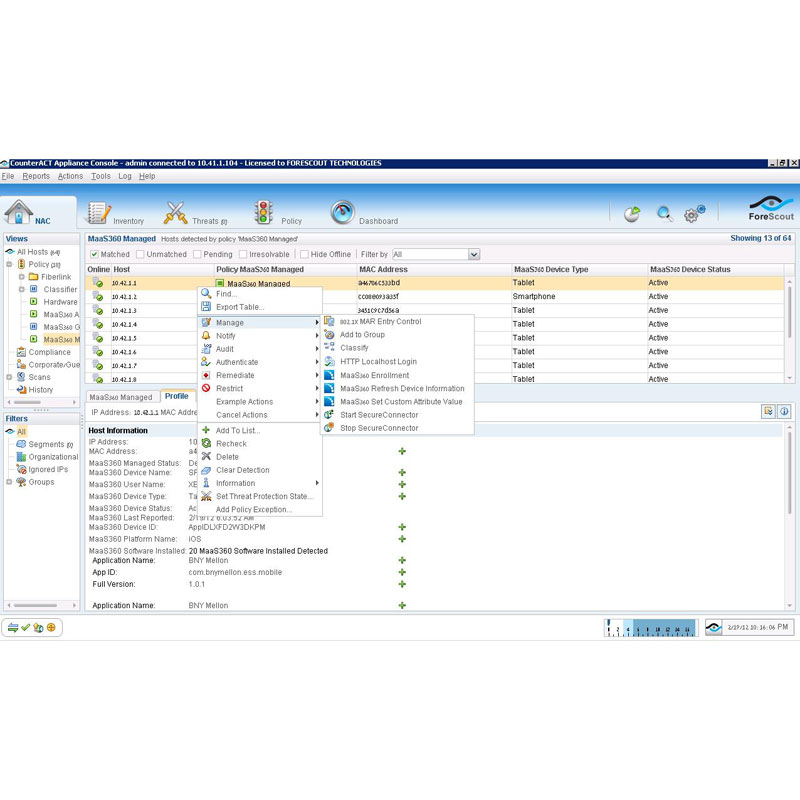
- SecureConnector™ SecureConnector is a small-footprint executable that runs on the endpoint. It reports endpoint information back to Forescout eyeSight, and implements Forescout actions on the endpoint. The Start SecureConnector action initiates SecureConnector installation on endpoints.
- In the Forescout console, from the navigation bar select Tools Options. In the dialog that appears, from the categories section on the left, click Modules. In the main area of the dialog, from the drop-down menu, select Open Integration Module.
This topic provides instructions on how to integratethe third-party device ForeScout CounterACT with Juniper NetworksSoftware-Defined Secure Networks (SDSN) solution to remediate threatsfrom infected hosts for enterprises. ForeScout CounterACT is an agentlesssecurity appliance that dynamically identifies and evaluates networkendpoints and applications the instant they connect to your network.CounterACT applies an agentless approach and integrates with SDSNto block or quarantine infected hosts on Juniper Networks’ devices,third-party switches, and wireless access controllers with or without802.1x protocol integration.
To integrate ForeScout CounterACT with SDSN, you must createa connector in Policy Enforcer that enables CounterACT to connectto your secure fabric and create policies for CounterACT. Before youconfigure the ForeScout CounterACT connector, you must ensure thatForeScout CounterACT is installed and running with the Open IntegrationModule (OIM). The ForeScout OIM consists of two plug-ins: Data Exchange(DEX) and Web API. Install both the plug-ins and ensure that theyare running. You must configure these plug-ins before you create aconnector in Policy Enforcer.
If you do not have ForeScout CounterACT installed in your network,obtain an evaluation copy from here.
This topic includes the following sections:
Configuring the DEX Plug-in
The DEX plug-in receives API information about infected hostsfrom the ForeScout CounterACT connector. Messages from infected hostsare either blocked or quarantined.
When you configure the DEX plug-in, you also configure a newproperty, Test, for DEX. When configured, this property ensures thatWeb services are available for Policy Enforcer, monitors the networkstatus, and validates usernames and passwords.
- Select Options > CounterACTWeb Services > Add.
The Add page appears.
- In theName field, enter the name for the CounterACT Web service account.
Enter this name in the DEX User Role field (see Step 3) whileconfiguring the ForeScout connector in Security Director.
- In the Description field, enter a brief description ofthe purpose of the Web service account.
- In theUsername field, enter the username that will be used to authorizeCounterACT to access the Web service account.
- In thePassword field, enter the password that will be used to authorizeCounterACT to access this Web service account.
- Click Add.
The General pane of the Add Property from CounterACT Web Servicewizard opens, as shown in Figure 2.
- Add properties such as block, quarantine, and Test, asshown in Figure 3.
You must include the Test property. Otherwise, you cannot addCounterACT as a third-party connector to Policy Enforcer successfully.
- In the Security Settings tab, click OK. The IP address appears in the IP AddressRange list, as shown in Figure 5.
- On the Data Exchange (DEX) page, click
To configure the Web API plug-in:
Forescout Secure Connector Mac
- Select Options > Add.
The Add Credentials page appears.
- Use the same username and password that you created forthe DEX configuration (see Step 6 and Step 7) andclick Client IPs tab and click OK.
The IP address appears in the IP Address Range list, as shownin Figure 7.
- Click
Creating ForeScout CounterACT Connector in Security Director
After you configure the DEX and Web API plug-ins, you need tocreate a connector for ForeScout CounterACT in Policy Enforcer.
To create a ForeScout CounterACT connector in Junos SpaceSecurity Director:
- Select Administration > Connectors.
The Connectors page appears.
- Click the create icon (+).
The Create Connector page appears.
- In theGeneral tab, select ForeScout CounterACT as the connector type andprovide the username, DEX user role, and password, as shown in Figure 8. ( The DEX user role isthe one that you created in Step 4).
Specify 443 as the port number for communication.
- In the Network Details tab, configure the IP subnets,as shown in Figure 9.
CounterACT treats the IP subnets as endpoints and takes action.
- In the Configuration tab, specify the Web API usernameand password, as shown in Figure 10.
- Click Forescout Secureconnector Mac
Infected Host Policy Enforcer Action
Connection State
Action Performed by CounterACT
Blocked
Wired
Apply access control list (ACL) to block inbound andoutbound traffic for a specific MAC address.
Wireless
Apply WLAN block on the endpoint, which will block thetraffic based on the wireless MAC address.
Dot1x
Apply CoA.
Quarantined
Wired
Apply VLAN. This action is specified by Policy Enforcer.
Wireless
Apply VLAN. This action is specified by Policy Enforcer.
Related Documentation
Findings (MAC III - Administrative Sensitive)
Finding ID Severity Title Description V-233333 High Forescout that stores device keys must have a key management process that is FIPS-approved and protected by Advanced Encryption Standard (AES) block cipher algorithms. The NAC that stores secret or private keys must use FIPS-approved key management technology and processes in the production and control of private/secret cryptographic keys. Private key data is ... V-233312 High If a device requesting access fails Forescout policy assessment, Forescout must communicate with other components and the switch to either terminate the session or redirect the endpoint to the remediation subnet. Endpoints with identified security flaws and weaknesses endanger the network and other devices on it. Isolation or termination prevents traffic from flowing with traffic from endpoints that have ... V-233311 High For endpoints that require automated remediation, Forescout must be configured to redirect endpoints to a logically separate VLAN for remediation services. Automated and manual procedures for remediation for critical security updates will be managed differently. Continuing to assess and remediate endpoints with risks that could endanger the network ... V-233310 High Endpoint policy assessment must proceed after the endpoint attempting access has been identified using an approved identification method such as IP address. Automated policy assessments must reflect the organization's current security policy so entry control decisions will happen only where remote endpoints meet the organization's security ... V-233315 High Forescout appliance must not be configured to implement a DHCP layer 3 method for separation or device authorization. An internal rogue device can still bypass the authentication process, regardless of the policy flow. Configuring the NAC to process all device authentication will ensure that any rogue device, ... V-233314 High Forescout must be configured so that all client machines are assessed by Forescout with exceptions that are allowed to bypass Forescout based on account or account type, as approved by the Information System Security Manager (ISSM) and documented in the System Security Plan (SSP). The NAC gateway provides the policy enforcement allowing or denying the traffic to the network. Unauthorized traffic that bypasses this control presents a risk to the organization's data and ... V-233318 High Forescout must place client machines on the blacklist and terminate Forescout agent connection when critical security issues are found that put the network at risk. If a device communicates outside of its normal required communication, this could be suspect traffic and should be stopped and proper individuals notified immediately. V-233340 High When connecting with endpoints, Forescout must validate certificates used for Transport Layer Security (TLS) functions by performing RFC 5280-compliant certification path validation. A certificate's certification path is the path from the end entity certificate to a trusted root certification authority (CA). Certification path validation is necessary for a relying party to ... V-233309 High Forescout must enforce approved access by employing admissions assessment filters that include, at a minimum, device attributes such as type, IP address, resource group, and/or mission conditions as defined in Forescout System Security Plan (SSP). Successful authentication must not automatically give an entity access to an asset or security boundary. The lack of authorization-based access control could result in the immediate compromise and ... V-233339 Medium Forescout must use a bidirectional authentication mechanism configured with a FIPS-validated Advanced Encryption Standard (AES) cipher block algorithm to authenticate with the endpoint device. Bidirectional authentication provides stronger safeguards to validate the identity of other devices for connections that are of greater risk. Currently, DoD requires the use of AES for ... V-233338 Medium Forescout must deny network connection for endpoints that cannot be authenticated using an approved method. Without identifying devices, unidentified or unknown devices may be introduced, thereby facilitating malicious activity. Identification failure does not need to result in connection termination or ... V-233331 Medium For TLS connections, Forescout must automatically terminate the session when a client certificate is requested and the client does not have a suitable certificate. In accordance with NIST SP 800-52, the TLS server must terminate the connection with a fatal “handshake failure” alert when a client certificate is requested and the client does not have a ... V-233330 Medium Forescout switch module must only allow a maximum of one registered MAC address per access port. Limiting the number of registered MAC addresses on a switch access port can help prevent a CAM table overflow attack. This type of attack lets an attacker exploit the hardware and memory ... V-233332 Medium Forescout must use TLS 1.2, at a minimum, to protect the confidentiality of information passed between the endpoint agent and Forescout for the purposes of client posture assessment. Using older unauthorized versions or incorrectly configuring protocol negotiation makes the gateway vulnerable to known and unknown attacks that exploit vulnerabilities in this protocol. V-233335 Medium Forescout must generate a log record when the client machine fails policy assessment because required security software is missing or has been deleted. Generating log records with regard to modules and policies is an important part of maintaining proper cyber hygiene. Keeping and maintaining the logs helps to establish, correlate, and investigate ... V-233334 Medium Communications between Forescout endpoint agent and the switch must transmit access authorization information via a protected path using a cryptographic mechanism. Forescout solution assesses the compliance posture of each client and returns an access decision based on configured security policy. The communications associated with this traffic must be ... V-233337 Medium Forescout must perform continuous detection and tracking of endpoint devices attached to the network. Continuous scanning capabilities on the NAC provide visibility of devices that are connected to the switch ports. The NAC continuously scans networks and monitors the activity of managed and ... V-233336 Medium Forescout must be configured with a secondary log server, in case the primary log is unreachable. It is critical for the appropriate personnel to be aware if a system is at risk of failing to process audit logs as required. Without this notification, the security personnel may be unaware of an ... V-233313 Medium Forescout must be configured to notify the user before proceeding with remediation of the user's endpoint device when automated remediation is used. Connections that bypass established security controls should be allowed only in cases of administrative need. These procedures and use cases must be approved by the Information System Security ... V-233317 Medium When devices fail the policy assessment, Forescout must create a record with sufficient detail suitable for forwarding to a remediation server for automated remediation or sending to the user for manual remediation. Notifications sent to the user and/or network administrator informing them of remediation requirements will ensure that action is taken. V-233316 Medium Forescout must send an alert to the Information System Security Manager (ISSM) and System Administrator (SA), at a minimum, when critical security issues are found that put the network at risk. Requiring authentication and authorization of both the user's identity and the identity of the computing device is essential to ensuring a non-authorized person or device has entered the network. V-233319 Medium Forescout must be configured so client machines do not communicate with other network devices in the DMZ or subnet except as needed to perform a client assessment or to identify itself. Devices not compliant with DoD secure configuration policies are vulnerable to attack. Allowing these systems to connect presents a danger to the enclave.Verify that Forescout is not allowed to ... V-233326 Medium Forescout must authenticate all endpoint devices before establishing a connection and proceeding with posture assessment. Authenticating all devices as they connect to the network is the baseline of a good security solution. This is especially important prior to posture assessment to ensure authorized devices are ... V-233327 Medium Forescout must be configured to apply dynamic ACLs that restrict the use of ports when non-entity endpoints are connected using MAC Authentication Bypass (MAB). MAB is only one way of connecting non-entity endpoints, and can be defeated by spoofing the MAC address of an assumed authorized device. By adding the device to the MAB, the device can then gain ... V-233324 Medium Forescout must off-load log records onto a different system. Having a separate, secure location for log records is essential to the preservation of logs as required by policy. V-233325 Medium Forescout must generate a critical alert to be sent to the Information System Security Officer (ISSO) and Systems Administrator (SA) (at a minimum) in the event of an audit processing failure. Ensuring that a security solution alerts in the event of misconfiguration or error is imperative to ensuring that proper auditing is being conducted. Having the ability to immediately notify an ... V-233322 Medium Forescout must deny or restrict access for endpoints that fail critical endpoint security checks. Devices that do not meet minimum-security configuration requirements pose a risk to the DoD network and information assets.Endpoint devices must be disconnected or given limited access as ... V-233323 Medium Forescout must be configured to log records onto a centralized events server. Keeping an established, connection-oriented audit record is essential to keeping audit logs in accordance with DoD requirements. V-233320 Medium Forescout must enforce the revocation of endpoint access authorizations when devices are removed from an authorization group. Ensuring the conditions that are configured in policy have proper time limits set to reflect changes will allow for proper access. This will help to validate that authorized individuals have ... V-233321 Medium Forescout must enforce the revocation of endpoint access authorizations at the next compliance assessment interval based on changes to the compliance assessment security policy. This requirement gives the option to configure for automated remediation and/or manual remediation. A detailed record must be passed to the remediation server for action. Alternatively, the ... V-233328 Medium Forescout must reveal error messages only to the Information System Security Officer (ISSO), Information System Security Manager (ISSM), and System Administrator (SA). Ensuring the proper amount of information is provided to the Security Management staff is imperative to ensure role based access control. Only those individuals that need to know about a security ... V-233329 Medium Forescout must configure TCP for the syslog protocol to allow for detection by the central event server if communications is lost. It is critical for the appropriate personnel to be aware if a system is at risk of failing to process audit logs as required. Without this notification, the security personnel may be unaware of an ...
- Select Administration > Connectors.
- Select Options > Add.